An easy-to-exploit bug in a popular WordPress plugin caused an internet-wide wave of hacking. Defiant, the company behind the Wordfence web firewall, said on Friday that millions of WordPress sites were hacked this week. The spike in attacks is due to the fact that hackers discovered a zero-day vulnerability in “File Manager“, a popular WordPress plugin installed on more than 700,000 sites, and started using it.
With this zero-day vulnerability, an attacker could upload malicious files without being authenticated to a site running an older version of the File Manager plug-in.
How hackers discovered zero-day is not yet clear, but since the beginning of last week, attackers have begun searching for sites where this plugin might have been installed. As a result of this investigation, when a site suitable for the attack is found, the attackers load a web shell hidden inside an image file on the victim’s server. They then access this web shell and hijack the site, then lock it in a botnet.
Hackers are on the Hunt
“Attacks against this vulnerability have increased significantly in the past few days,” said Ram Gall, Defiant’s Threat Analyst. In the early days of the vulnerability, the attacks started relatively slowly, but on Friday, September 4th, one million WordPress sites saw attacks, according to Defiant’s records. Throughout the week, attacks grew like an avalanche. Ram Gall stated that since the attacks were first discovered on September 1, more than 1.7 million sites have been attacked by Defiant.
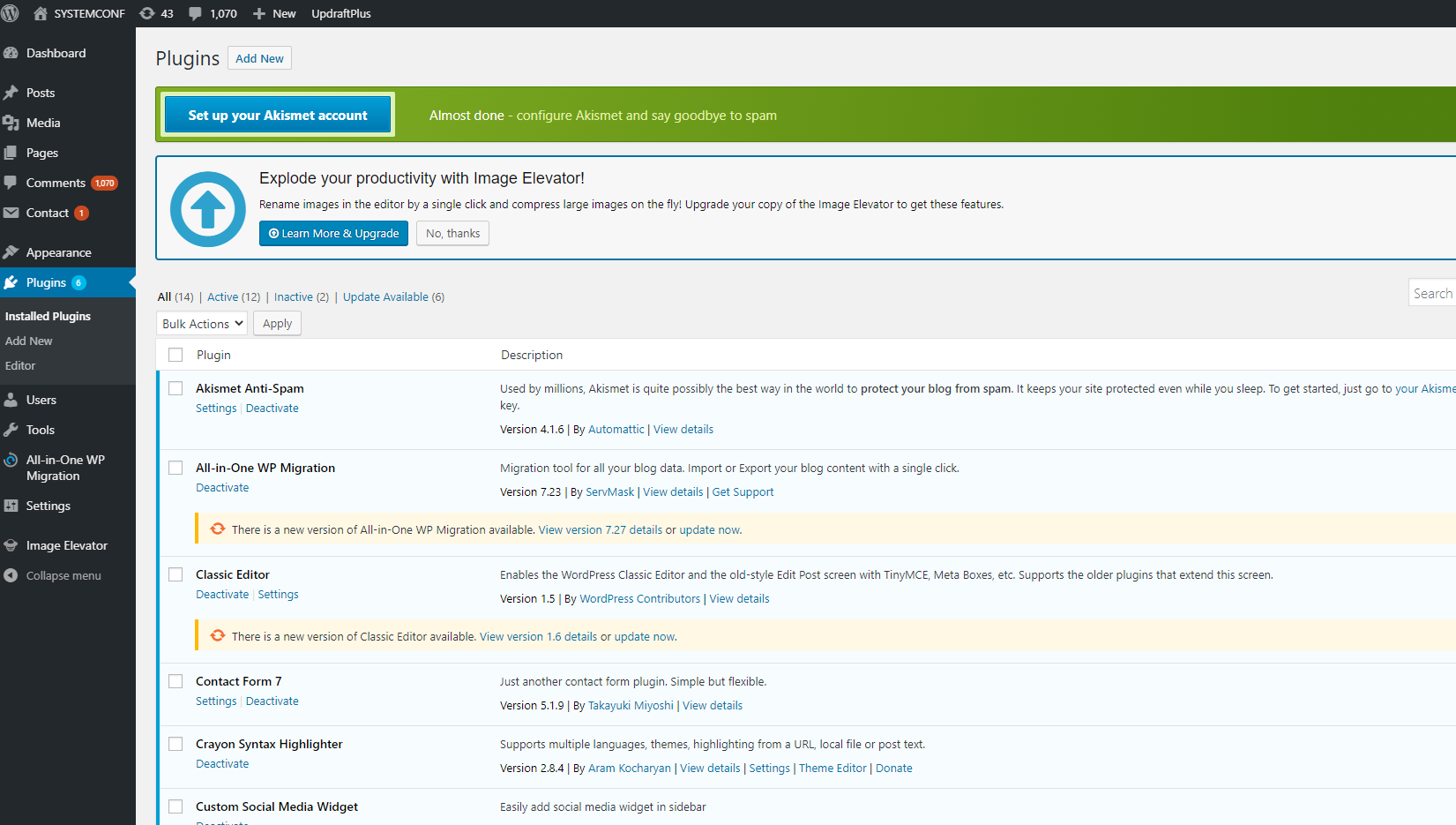
Wordfence Premium users and users with the Free version are protected against this attack by the built-in file upload protection of the Wordfence firewall. To protect your site from this vulnerability, your Wordfence firewall needs to be optimized. Wordfence Premium customers received this new firewall rule on September 1, 2020, at 14:56 (UTC). Free Wordfence users will receive this rule after thirty days on October 1st, 2020.
Description: Remote Code Execution
Affected Attachment: File Manager
Plugin Slug: wp-file-manager
Affected Versions: 6.0-6.8
CVSS Score: 10.00 (Critical)
CVSS Vector: CVSS: 3.0 / AV: N / AC: L / PR: N / UI: N / S: C / C: H / I: H / A: H
Patched Versions. 6.9
The 1.7 million figure is more than half of WordPress sites using the Wordfence web firewall. Gall believes the true scale of the attacks is much greater, as WordPress is installed on hundreds of millions of sites. With the spread of vulnerability, probably all of these sites will be targeted by attackers in the coming days.
Fortunately, the day the File Manager developer team found out about the attacks, they created and released a zero-day patch and prevented the attacks. Some site owners have installed the patch, but as usual, the majority did not install the updates in time.
It is this slowness of patching that has recently prompted the WordPress development team to add an auto-update feature for WordPress themes and plugins. Since WordPress 5.5 released last month, site owners can configure plugins and themes to automatically update their site whenever a new update is available and can be sure that their site is always running the latest version of a theme or plugin and is safe from attacks.
Recommendations to Users from the Wordfence Team
- When using utility add-ons such as this file manager, you should take the utmost precaution.
- In order for attackers to increase their privileges, you should uninstall utility add-ons when not in use, such as file management plug-ins, so that they do not create an easy intrusion vector.
- The vulnerability itself could allow a remote, unauthenticated user to execute commands and upload malicious files to the target site. Therefore, Gall recommends users to fix the problem by installing the latest version of the plugin, v6.9.
- If you are not actively using the plugin, uninstall it completely.