There are two types of approaches in today’s information security. A proactive approach is generally accepted. Penetration tests and vulnerability assessment are one of the most important components of proactive security.
Pentest and vulnerability assessment are similar but different concepts. Vulnerability scanning is the process of finding and reporting security vulnerabilities in the target system using various software.
In pentest studies, the aim is not only to identify security vulnerabilities but to determine additional operations (infiltration into the system, access to database information) that can be performed on the target systems using these vulnerabilities.
Vulnerability scanning is mostly performed using automated tools and takes a short time. Pentest studies, on the other hand, are a process that requires an advanced level of experience, including the weakness scanning step, and the detected vulnerabilities are examined and special reports are presented to the customers, taking much longer than the weakness scanning studies.
Note: Vulnerability scanning is mostly performed using automated tools and takes a short time. Pentest studies, on the other hand, are a process that requires an advanced level of experience, including the weakness screening step, and the detected vulnerabilities are examined and special reports are presented to the customers, taking much longer than the vulnerability scanning studies.
How to Make a Web Pentest?
Our tests are carried out independently of the platform and development language (PHP, Ajax, JavaScript, JSP, Java, ASP, ASP.NET, Cold Fusion, Perl, Flash and Ruby) used in the target system. Manual tests are more prominent in pentest studies. Automated tools are generally used to speed up transactions and to obtain additional information after infiltration (such as determining the database structure after Sqli and downloading data), which is called post-exploitation. The tests to be performed can be in two different forms depending on the company’s request.
- BlackBox Pentest
- WhiteBox Pentest
BlackBox Web Pentest Method
The only information about the application to be tested is the web page of the application. The purpose of this method is to completely examine the web application from the outside with a third eye and to determine the vulnerabilities and what types of attacks it is vulnerable to.
Whitebox Web Pentest Method
In this method, the tests are started by getting as much detailed information as possible about the target application. The most important information to be obtained from the company that will undergo testing is the web application test username and test password to be tested.
Web Penetration Tests Details Application Discovery and Information Gathering Step
First, the discovery of the application is carried out. At this stage, the aim is to extract the files and directories that can be found directly and not directly linked to the target web application, and to fully define the application in the target system. The step-by-step information-gathering phase is as follows.
- Determining the TCP ports on which the target application is running.
- Determination of other web applications running in the target system.
- Mapping the target web application – OWASP-IG-001.
- Collecting information about the target system in different search engines (Google, Shodan etc) OWASP-IG-002.
- Determination of application input points – OWASP-IG-003.
- Signature scanning for known web software – OWASP-IG-004.
- Identifying and analyzing error messages – OWASP-IG-006.
- Determination of software version information used for a target web application, web server and web service.
Web Pentest Attack Trials
In the Web Pentest attack trials, 66 attack attempts are carried out in nine different categories.
- SSL / TLS version, algorithm and certificate validity tests – OWASP-CM-001.
- Determining the management panel used in the target application – OWASP-CM-00.
- File extension management tests – OWASP-CM-005.
- Identifying backup, copy, test or legacy pages and applications – OWASP-CM-00.
- Determination of methods supported by the server and XST – OWASP-CM-008.

Authentication Tests
- Transfer of sensitive information over encrypted / unencrypted channels – OWASP-AT-001.
- Username determination / verification studies on target application – OWASP-AT-002.
- Identifying users defined in the target application – OWASP-AT-00.
- Brute force password attempts to authorized users on the target application – OWASP-AT-00.
- Attempts to circumvent the authentication phase – OWASP-AT-005.
- Tests of password reminder and password reset features – OWASP-AT-006.
- Browser cache management and tests of “Log out” functions – OWASP-AT-007.
- CAPTCHA safety tests – OWASP-AT-008.
Session Management Tests
- Session management weaknesses, session management bypass tests – OWASP-SM-001.
- Detailed cookie security tests – OWASP-SM-002.
- Session fixation tests – OWASP-SM-003.
- Session values prediction attacks – OWASP-SM-004.
- CSRF (Cross-site request forgery) tests – OWASP-SM-005.
Authorization Tests
- Directory Traversal tests – OWASP-AZ-001.
- Authorization bypass, authorization pass tests – OWASP-AZ-002.
- Authorization escalation tests – OWASP-AZ-003.
Business Logic Control Tests
- Testing of non-technical attacks for the functioning of the application after determining the operation of the application.
Data Verification Tests
- Projected XSS tests – OWASP-DV-001.
- Stored XSS tests – OWASP-DV-002.
- DOM-based XSS tests – OWASP-DV-003.
- XML (Flash XSS) tests -OWASP-DV-004.
- SQL injection tests – OWASP-DV-005.
- LDAP injection tests – OWASP-DV-006.
- XNL tests – OWASP-DV-008.
- Xpath injection tests – OWASP-DV-010.
- Code injection tests – OWASP-DV-012.
- Operating system command injection tests – OWASP-DV-013.
- Buffer overflow tests – OWASP-DV-014.
- Http response splitting tests – OWASP-DV-016.
Denial of Service Tests
- Testing for SQL Wildcard Attacks (OWASP-DS-001).
- Testing for DoS Locking Customer Accounts (OWASP-DS-002).
- Testing for DoS Buffer Overflows (OWASP-DS-003).
- Testing for DoS User Specified Object Allocation (OWASP-DS-004).
- Testing for User Input as a Loop Counter (OWASP-DS-005).
- Testing for Writing User Provided Data to Disk (OWASP-DS-006).
- Testing for DoS Failure to Release Resources (OWASP-DS-007).
- Testing for Storing too Much Data in Session (OWASP-DS-008).
Web Service Tests
- Web service information gathering efforts – OWASP-WS-001.
- WSDL tests – OWASP-WS-002.
- XML structure tests – OWASP-WS-003.
Ajax Tests
- AJAX Vulnerabilities (OWASP-AJ-001).
- How to test AJAX (OWASP-AJ-002).
Tests of Web Application Security Systems
- Web application firewall exploration tests.
- Network IPS exploration tests.
- IPS / Web application firewall circumvention tests.
Web Pentest Risk Leveling
This technical report, which will contribute directly to the risk analysis procedure, is based on the following classical formula used in risk calculation.
ASSET VALUE x (THREAT x PROBABILITY x VULNERABILITY)
In the above calculation, the value of the asset will be left to the risk analysis procedure, and the second multiplier in the brackets will be used in the levelling of the openings in this technical report. Threat, Probability and Vulnerability phenomena are described below.
- The threat is the potential of any threat source to damage assets, either intentionally or accidentally using a vulnerability.
- Vulnerabilities are weaknesses, errors or defects in system security procedures, design, implementation of internal controls that may cause information security violations.
- Probability is the probability of threats and vulnerabilities in the current environment. In probability calculation, Error! Reference source not found. The part mentioned in the section and explaining the possible realization point of the opening found in detail will be used.
With the THREAT x PROBABILITY x VULNERABILITY calculation, the vulnerabilities found in penetration and inspection studies were evaluated in five risk ranges for the ease of reading the levels. Thus, these values should match, for example, with the five-level risk values used in the PCI-DSS security scanning procedures document.
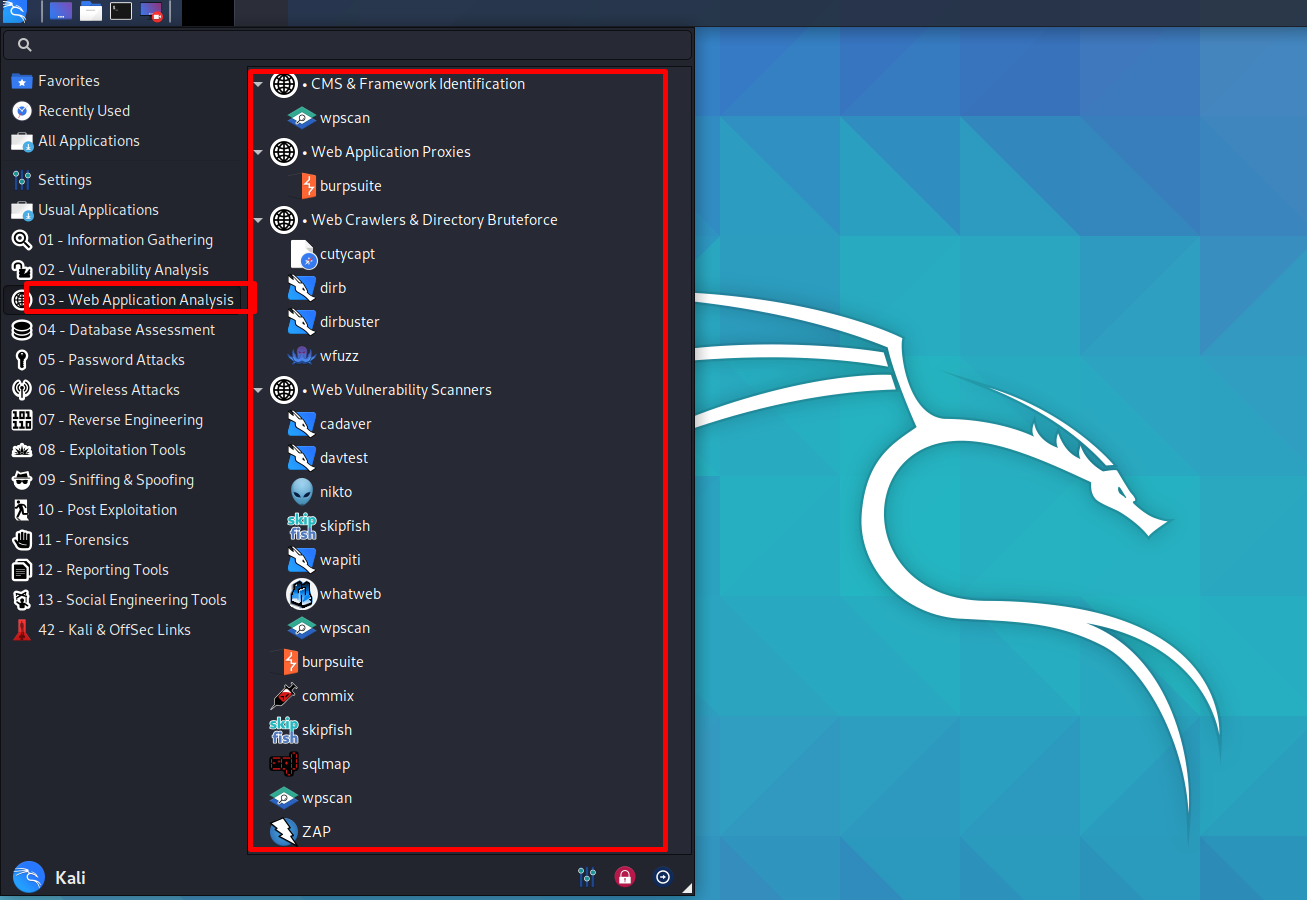
Software Used in Web Application Pentest Studies
You can use commercial, open-source and self-developed software/tools.
Commercial Software Used
- Netsparker
- Metasploit Pro
- Acunetix
- IBM AppScan
- Rapid7 Nexpose
Open Source / Free Software and Components Used
- Nessus
- Nessus
- TamperData
- Add N Edit Cookies
- WebScarab
- Burp Suite
- OWASP ZAP Proxy
- w3af
- Webscarab
- Nikto
- Dirbuster
- Medusa, Hydra
- sqlmap
- Backtrack 5
- HP SWFScan
- SamuraiWTF (Web Testing Framework)
- Metasploit
Web Pentest Reporting
One of the most important components of the Pentest study is the reporting part. Special attention should be paid to reporting and to ensure that all findings written in the report are not false positives. Considering that the report will be read not only by the technical staff but also by the managers, the introduction part of the report should be prepared as an executive summary to include the conclusion of the work and the work done. In addition, the reference information of all the gaps, the details of the infiltration steps, if any, and the commands/tools used and the actions to be taken to close the gap should be written in a simplicity that will not bore and confuse those who read the report.