Active Directory is a directory service designed by Microsoft specifically for Windows Server and Client computer systems, which contains information such as a server, client computer, user and printer. With the Group Policy management tool included in this service, we can make various restrictions or distribute the application we want from a single point. It is a very preferred service because it provides great convenience in terms of centralizing the control and management of resources.
Active Directory first entered our lives with Windows Server 2000. In time, it has improved itself in the 2003, 2008 and 2012 systems and has taken its current form. All query and change operations and operations such as database management are carried out by the database engine called ESE (Extensible Storage Engine).
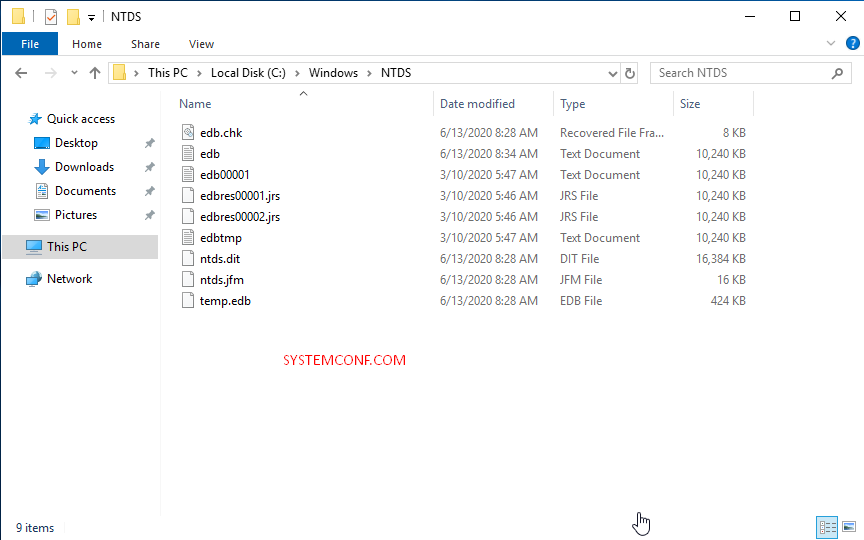
Active Directory service is kept on the server or servers called Domain Controller. The default location of the relevant service is “% systemroot% NTDS“. The database file name is ntds.dit (New Technology Directory Service-Directory Information Tree). However, the file named edb.log, which is called transaction log, where all transactions are temporarily involved, the changes are stored for various reasons before being written to the database, also plays a critical role in the operation of the Active Directory service. Another important database component is the ebd.chk file, which we can call ESE checkpoint. The task of this file is to check whether the change information written to edb.log can be written properly and consistently into “ntds.dit”.
Active Directory Features
- Manageability
- Scalability
- Expandability
- Security Integration
- Interoperability with Other Directory Services
- Secure Authentication and Authorization
- Management with Group Policy
- Ability to Work with Services like DNS and DHCP
Active Directory FSMO Roles (Flexible Single Master of Operation)
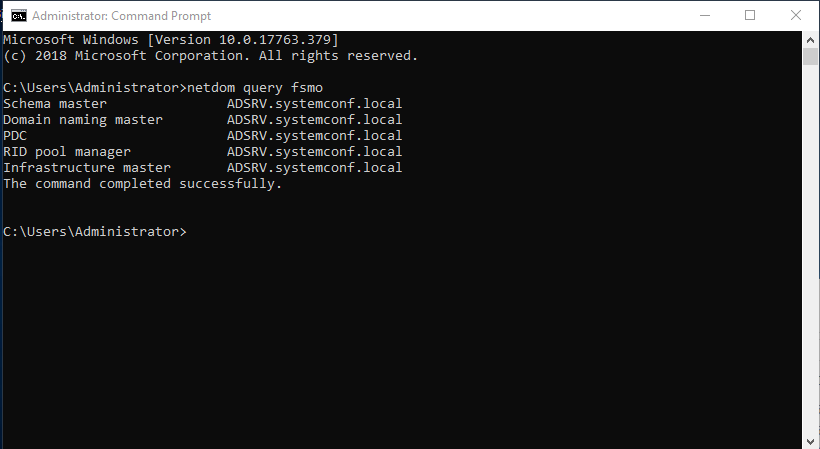
There are 5 roles on an Active Directory server. These;
- Schema Master
- Domain Naming Master
- PDC Emulator
- RID Master
- Infrastructure Master
It shaped. You can list these roles with the command “netdom query fsmo”.
netdom query fsmo
Schema Master
It is the component that determines the properties of objects in the structure in Active Directory Domain Services. We can say that it determines the formal structure of objects. For example, Schema determines that there will be information such as name, surname, city, task in the user object. Only members of the Domain Admins and Enterprise Admins group have authority over this role.
Domain Naming Master
We can say that it is the guide that holds the domain names. This role gives confirmation of the name when a new domain will be established. Prevents name conflict.
RID Master
All objects on the network have a unique (unique) SID number. Allows objects to get a unique SID number and prevents conflict.
Infrastructure Master
It makes adjustments regarding the SID number of users from different domains. It provides replication with the Global Catalog server.
PDC Emulator
It provides replication between DCs on the network. Controls Windows sessions.
Active Directory Logical Structure
Domain
The domain is the most basic component of Active Directory. The domain must be created by selecting a unique name by the system administrator. In addition, Domains have certain limits in the security point. If the system administrator also has not set permission, the rights of a user will only apply within that Domain. Each domain has its own security structure.
Domains are also called replication units. Domain Controllers that contain Active Directory database copies in a Domain replicate these coils by replacing the changes made within the Domain.
Organizational Unit
Organizational Unit is objects created to organize users, groups or computers within a Domain. You can use it to group objects to meet the needs of the organization and to facilitate management.
For example, managerial requirements can be prioritized when grouping objects. In the organization, if one administrator is responsible for users and the other manager is responsible for computers, two OUs are created, one for users and one for computers, and computers are collected in one user and the other. Finally, both managers can be appointed separately. Or departmental groupings can be made. For example, an OU is created for “Accounting” and “Marketing” departments, and after the users working in these departments are placed in the relevant OUs, department chiefs can be assigned to these units as managers. These processes will also facilitate the work of us system administrators.
Tree and Forest
The first Windows Server Domain created refers to the Root Domain in the Active Directory structure. The new additional Domains to be created after that will create the logical Tree or Forest structure of the array.
Tree
When a new Domain is added in a Tree structure, the newly added Domain becomes the Child Domain of the Domain it was added from, and the Domain to which it is added becomes the Parent Domain for the added Domain. The name of the newly created Child Domain is combined with the name from the Parent Domain and the DNS name of the newly created Domain appears.
For example “omersivka.local” is a Root Domain. A new Domain to be added to this Domain will be the Child Domain of the “omer.local” Domain. As an example, we can show “mail.omer.local” Domain. In this example, mail.omer.local will be the Child Domain of the omer.local Domain. omer.local Domain is the Parent Domain.
Forest
Forest is the unified state of more than one Tree. The first Domain created refers to a Tree and is created in the Forest with the creation of the first Tree. Trees that will be added to this Forest later will have the same Schema and Global Catalog, although they will not share the same namespace with other Trees. The first Tree that was established while creating Forest is known as Forest-Root, and other Trees are gathered under this Forest Root.
Global Catalog
Global Catalog (GC) is a database containing every object in Active Directory Forest and is kept in Global Catalog Servers. These hosted features, by default, are the most commonly used features during queries. Global Catalog provides users with the following services;
• Provides information about Active Directory objects, regardless of where the required data is located.
• Uses Universal Group Membership information when logging into a network.
The Global Catalog Server is a Domain Controller on the Domain, and the first Domain Controller created on the Domain is automatically upgraded to the Global Catalog level. Additional Global Catalog Servers can be added later.

Active Directory Schema
It contains information about all objects such as users, groups, computers and printers. There is only one Schema in the Forest and all object information is written on this Schema. For example, we can give information such as departments where users work and birthplace. Schema information is stored in the Active Directory database (database).
• It offers a dynamic structure for user applications. Object search operations of the users take place via Schema.
• The newly created or modified object is dynamically updated in Schema.
• Discretionary access control lists (DACLs) are used to protect object classes and properties.
With DACLs, only authorized users can make changes to Schema.

Lightweight Directory Access Protocol (LDAP)
By definition, LDAP is the application layer protocol used to query and change directory services running on TCP / IP. It is a basic directory service protocol used for querying and updating (update) within the Active Directory architecture. With LDAP, Active Directory objects are redefined in Active Directory using OU (Organizational Unit) and CN (Common Name). LDAP nomenclature method; It is used to access Active Directory objects and contains two definitions;
• Distinguished Names
• Relative Distinguished Names
Distinguished Names
All Active Directory objects have a distinguished name with a complete path that allows them to be reached in a network environment. For example;
CN = Omer Sivka, OU = Technique, DC = osivka, DC = local
CN Common Name used here means OU Organizational Unit and DC means Domain Controller. DC sets the Domain hierarchy. All DNS flow is written one by one. For example; If the domain name is osivka.local, it is specified as DC = osivka, DC = local. To give another example, if the user named “ASAF” is in the OU named “BLACK” and its domain name is “osivka.local”. Its “Distinguished Name” software will be as follows;
CN = ASAF, OU = BLACK, DC = osivka, DC = local
Relative Distinguished Name
It is located in the LDAP distinguished name and includes the unique identification of the object. That is, it is unique in the Domain specified in Active Directory. For example;
CN = SIVKA, OU = WHITE, DC = osivka, DC = local
The only one in osivka.local software is the Relative Distinguished Name AKIF. The most recent value is always a single value. Therefore, it cannot be repeated.
Active Directory Physical Structure
The physical structure in Active Directory has an architecture-independent of logical structure. While organizing network resources with logical structure, control and configuration of network traffic can be realized with physical structure. The physical structure of Active Directory; Creates DC (Domain Controller) and Sites. The physical structure of Active Directory determines the location and time of the replication and its logon. Optimization of network traffic and logon processes and elimination of errors in these processes depend on understanding the physical structure.
Domain Controller
Domain Controller is the server that has a copy (replica) of the Active Directory database on it. Any changes made to the Domain are done on a Domain Controller and then all Domain Controllers in the domain copy these changes to each other through replication. Domain Controllers hold directory information and execute users’ log operations, authentication processes, and directory searches. There can be one or more Domain Controllers in a Domain. In a small organization, one Domain Controller and Additional Domain Controller are sufficient, while for a large business spread across different physical locations, one or two Domain Controllers per region would be more appropriate. The purpose of placing multiple Domain Controllers in a Domain is both to provide error tolerance and to distribute loads between Domain Controllers.
Sites
A Site refers to one or more IP subnets connected to each other by high-bandwidth outlines. By configuring the sites correctly, we can enable Active Directory to use the physical connections between subnets in the most effective way to minimize the network traffic that occurs in logon processes and the intensity that occurs during replication processes. The main reasons for creating a site are:
• Optimizing replication traffic
• Users can find the right Domain Controller using the fastest and most reliable connection during the logo.
Active Directory and DNS
Active Directory and DNS integration are one of the most important features of the Windows Server system. Active Directory and DNS have a similar hierarchical naming structure that can be presented as both Active Directory objects and DNS domains and resource records. As a result of this integration, computers on the Windows Server network use DNS servers to locate computers running certain services that are specific to Active Directory. For example, a client learns the IP address of the Domain Controller, which is required to be logon to Active Directory or to search any source (printer or shared folder) in the directory, from the SRV records on the DNS server. In order for Active Directory to run smoothly, DNS servers must host SRV records completely. The purpose of SRV records is to indicate the location of Domain Controllers to clients during logon or when accessing any source. In an environment without SRV records, clients will not be able to log into Domain. In addition, Windows Server allows the DNS information to be stored integrated with the Active Directory database. In this way, the replication of DNS information becomes more effective and secure.




